A data breach at Canada Computers has put a spotlight on one of the most common weak points in online retail: the guest checkout lane. The company says an unauthorized party accessed a system that supports its retail website, potentially exposing personal and payment information for customers who completed purchases without logging into a member account. For shoppers, the practical question is simple: who is affected, what information may have been exposed, and what does this incident reveal about how modern e-commerce attacks work.
What Canada Computers says happened: The retailer has described the incident as unauthorized access to an online system supporting its website. The company’s public updates indicate the exposure was tied to the guest checkout flow during a specific window, rather than to in-store transactions or purchases made while logged into a Canada Computers member account.
At-a-glance
- Incident involves online systems tied to the retail website, not in-store purchases.
- Customers who checked out as “guests” during the affected period are the primary group at risk.
- The company has said the information may include credit card details for those who did not log in while purchasing.
- Complimentary credit monitoring and identity protection have been offered to affected customers.
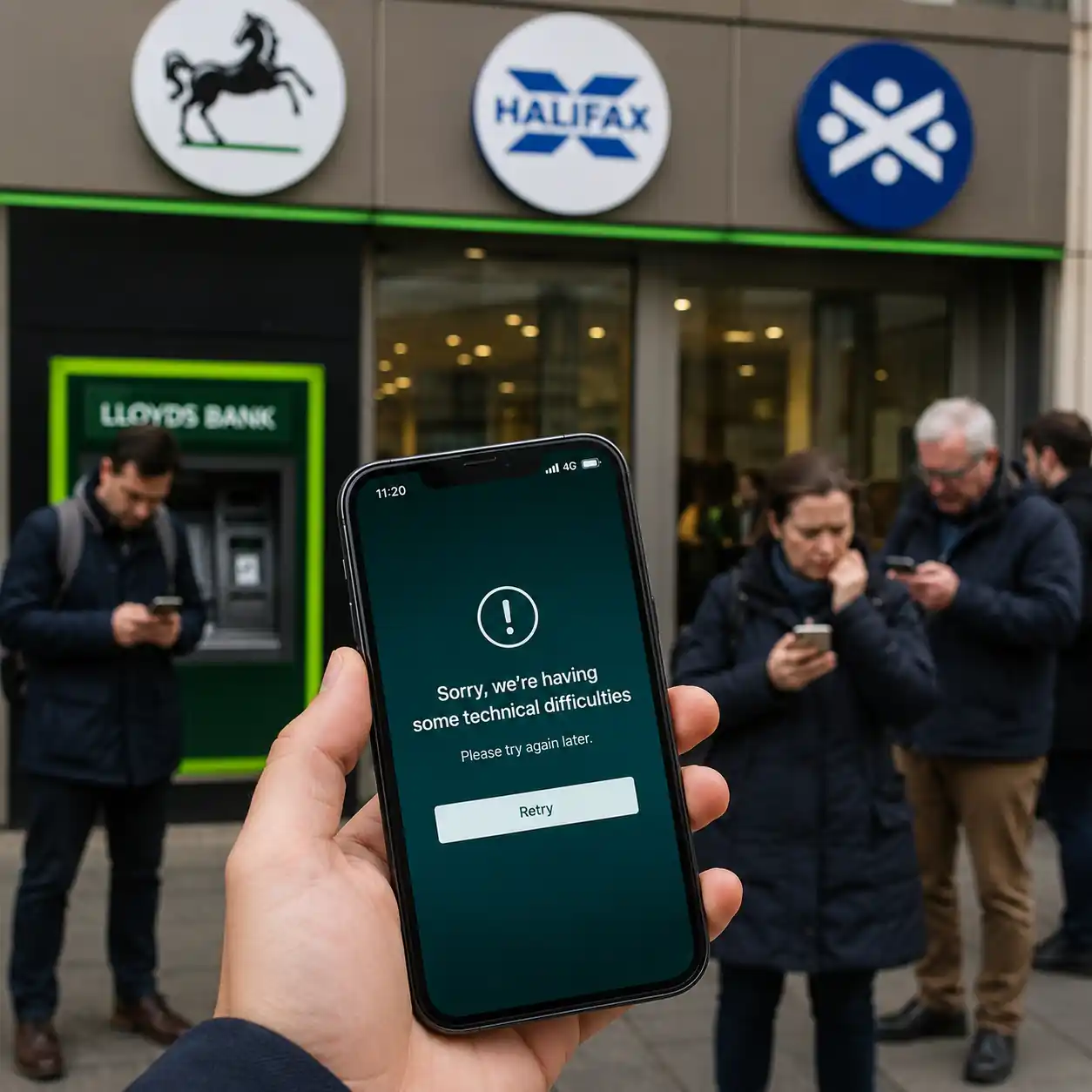
Why “guest checkout” is the key detail: In many retail setups, guest checkout is handled differently from logged-in accounts. It’s designed to remove friction and speed up purchases, but it can also mean fewer checks around user identity, less durable session tracking, and different data-handling paths. When attackers target payment pages, they often look for the simplest route that collects the most valuable information in one place: the moment a shopper types in card details, billing address, and contact information.
This is why “guest checkout” incidents can feel especially unsettling. You can do everything “normally,” finish a purchase, and still end up exposed if the checkout layer itself was compromised. In some cases, these attacks are linked to so-called “web skimmers,” where malicious code is inserted into a payment form to copy details as they are entered. The shopper’s bank may not see anything unusual until fraud attempts begin, which is why these breaches are often discovered after the fact.
What information may have been exposed: Based on the company’s descriptions and typical e-commerce checkout data flows, the exposed information can include contact and order details such as name, email address, phone number, billing address, and purchase information. Canada Computers has also indicated that credit card details may have been involved for customers who checked out as guests. While public disclosures do not always specify whether security codes were captured, the safest assumption for consumers is that any payment information entered during the affected period deserves heightened scrutiny.
Timeline that matters to shoppers: Canada Computers has said the affected group is tied to purchases made as guests between late December and late January, and it learned of unauthorized access on January 22. For customers, those dates matter more than the day the story hit headlines, because exposure risk is linked to when checkout information was submitted.
What customers typically look for next
- A clear confirmation of whether their order fell inside the affected date range.
- A description of what data fields were exposed, especially payment details.
- Whether the retailer is offering credit monitoring or identity protection, and for how long.
- Practical guidance that matches the risk: card monitoring, fraud alerts, and identity checks.
What this could mean in real life: The most common short-term risk after a checkout-linked breach is payment fraud, especially small “test” transactions followed by larger purchases if criminals believe a card is active. The longer-term concern is identity misuse if a combination of name, address, phone, and email is circulating. That doesn’t guarantee fraud will happen, but it can increase exposure to convincing phishing attempts, account takeover attempts at other retailers, or targeted scam calls that reference real purchase details.
A key nuance is that “member accounts not affected” does not automatically mean “customers are safe” if they shopped as guests. Many people default to guest checkout for one-off purchases, holiday shopping, or quick component buys. If you purchased during the stated window and you used guest checkout, that’s the group the company itself has placed at the center of the incident.
What this says about retail security in 2026: Retailers have steadily improved security around logins and account databases, but attackers have also adapted. Checkout pages remain attractive targets because they concentrate valuable details at the moment of payment. Even when companies secure their core databases, third-party scripts, plugins, and integrations can create risk if not tightly controlled. That’s why modern breach responses often include outside forensic investigation, law enforcement notification, and pressure to clarify the scope quickly for customers.
The other reality is communication: consumers judge breaches not only by what happened, but by how clearly the company explains it. In retail incidents, frustration often spikes when customers feel they have to guess whether they’re affected, cancel cards “just in case,” or learn key details through media coverage rather than direct notice.
For Canada, this case is also a reminder that breach notifications are not just a PR decision. Under Canada’s privacy rules, organizations are expected to assess whether a breach poses a “real risk of significant harm” and notify affected individuals when that threshold is met. Consumers, meanwhile, can treat official notifications and the retailer’s posted updates as the most reliable starting point for understanding exposure and next steps.
Canada Computers has said it is continuing its investigation and has offered complimentary credit monitoring and identity protection services to affected customers. If you are trying to verify the company’s stated timeline and what information may have been exposed, you can read the reporting that summarizes the company’s disclosure in this Canadian Press write-up.
For more consumer tech coverage and explainers, you can also browse Swikblog for the latest updates and practical breakdowns.